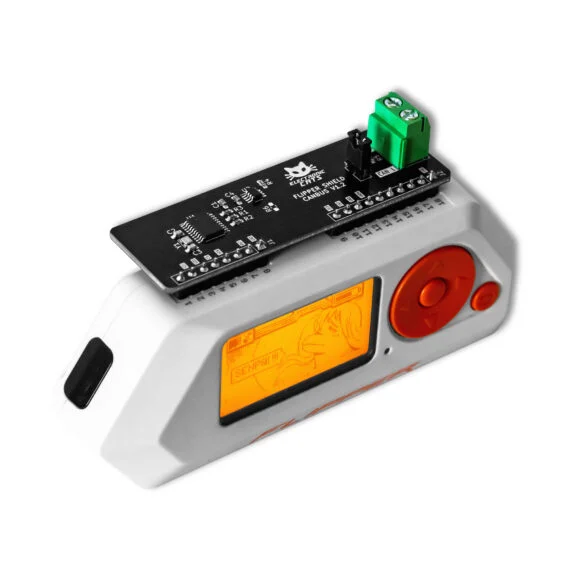
Evil Crow RF V2 – Multi-Radiofrequency Security Testing Tool
$69.29
$85.23
Evil Crow RF V2DisclaimerEvil Crow RF V2 is a basic device for professionals and cybersecurity enthusiasts.We are not responsible for the incorrect use of Evil Crow RF V2. The Evil Crow device is recommend using this device for professional testing and learning.Be careful with this device and the transmission of signals. Make sure to follow the laws that apply to your country.The Battery and card in the picture are just for showing which are not included in the package.IntroductionEvil Crow RF V2 is a radiofrequency hacking device for pentest and Red Team operations, this device operates in the following radiofrequency bands:300Mhz-348Mhz387Mhz-464Mhz779Mhz-928Mhz2.4GHzEvil Crow RF V2 has two CC1101 radiofrequency modules, these modules can be configured to transmit or receive on different frequencies at the same time. Additionally, Evil Crow RF V2 has a NRF24L01 module for other attacks.Evil Crow RF V2 allows the following attacks:Signal receiverSignal transmitterReplay attackURH parseMousejacking…NOTE:All devices have been flashed with basic firmware Evil Crow RF V2 before shipping.Please do not ask for new functions in this code. You can develop code for Evil Crow RF V2 and send PR with your new code.For more information please check the Evil Crow RF V2 Github repo:Firmware & InstallationThe basic firmware allows to receive and transmit signals. You can configure the two radio modules through a web panel via WiFi.Please see the GitHub repo for the latest steps (Updated since March 2026): https://github.com/joelsernamoreno/EvilCrowRF-V2RX Config ExampleModule: (1 for first CC1101 module, 2 for second CC1101 module)Modulation: (example ASK/OOK)Frequency: (example 433.92)RxBW bandwidth: (example 58)Deviation: (example 0)Data rate: (example 5)RX Log ExampleRAW TX Config ExampleModule: (1 for first CC1101 module, 2 for second CC1101 module)Modulation: (example ASK/OOK)Transmissions: (number transmissions)Frequency: (example 433.92)RAW Data: (raw data or raw data corrected displayed in RX Log)Deviation: (example 0)Binary TX Config ExampleModule: (1 for first CC1101 module, 2 for second CC1101 module)Modulation: (example ASK/OOK)Transmissions: (number transmissions)Frequency: (example 433.92)Binary Data: (binary data displayed in RX Log)Sample Pulse: (samples/symbol displayed in RX Log)Deviation: (example 0)Pushbuttons ConfigurationButton: (1 for first pushbutton, 2 for second pushbutton)Modulation: (example ASK/OOK)Transmissions: (number transmissions)Frequency: (example 433.92)RAW Data: (raw data or raw data corrected displayed in RX Log)Deviation: (example 0)URH Parse exampleDemo: https://youtube.com/watch?v=TAgtaAnLL6UOther SketchesMousejacking: EvilCrowRF-V2/firmware/other/standalone-mousejacking…Evil Crow RF V2 SupportYou can ask in the Discord group: https://discord.gg/jECPUtdrnWYou can open issue or send me a message via twitter (@JoelSernaMoreno).For more information please check the Evil Crow RF V2 Github repo: https://github.com/joelsernamoreno/EvilCrowRF-V2
Product Security & Research